What is OWASP?
OWASP stands for Open Worldwide Application Security Project and is a globally recognized, non-profit organization dedicated to improving software security. The goal of OWASP is to provide developers, companies, and security experts with freely accessible tools, documentation, and best practices to make applications more secure.
The community/OWASP community regularly publishes guides, tools, and training materials-one of the best-known projects is the OWASP Top Ten, a list of the ten most critical security risks for web applications.
The OWASP Top Ten
The OWASP Top Ten is a compilation of the most common and dangerous security vulnerabilities that occur in web applications. This list serves as an internationally recognized standard for developers and companies to identify, prioritize, and remedy security risks.
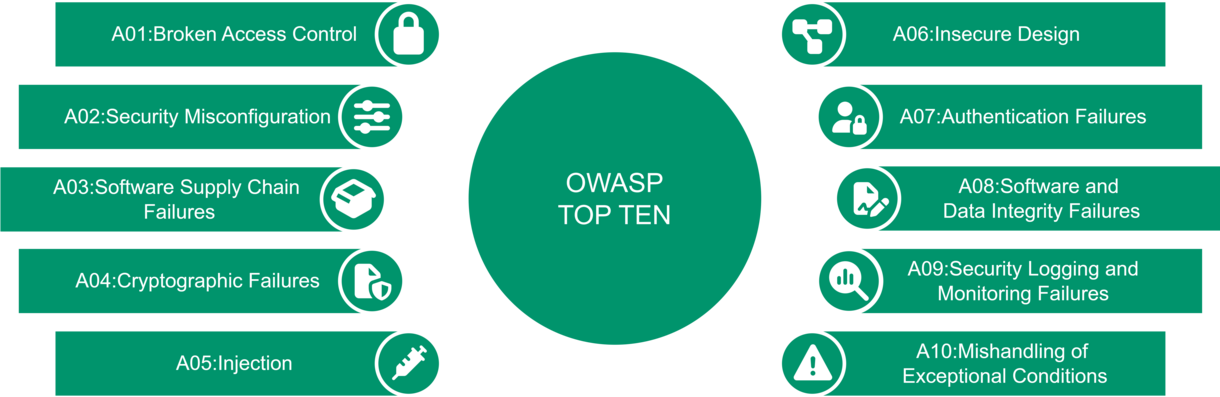
The categories from the current OWASP Top Ten (as of 2025) are:
- A01: Broken Access Control
Flaws in access control that allow unauthorized access. - A02: Security Misconfiguration
Misconfigurations of servers, frameworks, or databases. - A03: Software Supply Chain Failures
Security risks caused by insecure or compromised third-party components, libraries,
dependencies, or build pipelines (e.g., tampered updates or outdated libraries). - A04: Cryptographic Failures
Insecure or flawed implementations of encryption. - A05: Injection
Injection of malicious code (e.g., SQL, LDAP, or OS injection). - A06: Insecure Design
Insecure architectural decisions or lack of security principles. - A07: Authentication Failures
Vulnerabilities in login and session management. - A08: Software and Data Integrity Failures
Manipulation of data or software components. - A09: Security Logging and Monitoring Failures
Lack of monitoring and logging of attacks. - A10: Mishandling of Exceptional Conditions
Improper handling of error and exception conditions (e.g., through uncontrolled error messages, crashes, or the disclosure of sensitive system information during exceptions).
The OWASP Top Ten is regularly updated to reflect new threats and trends in the IT security landscape.
How we use OWASP in our security tests?
Our security tests are specifically based on the OWASP guidelines, in particular the OWASP Top Ten and the OWASP Web Security Testing Guide. This ensures that the tested applications are protected against the most common and dangerous attack scenarios.
imbus employees work on the basis of OWASP information, are members of the community, and regularly attend events such as regulars' tables, conferences, etc. In our security tests, OWASP standards are the minimum requirement for our approach.
Our approach includes, among other things:
- Automated scans with industry-standard tools (Burpsuite Professional, OWASP Zap, and many more).
- Manual security analyses and tests to identify (logical) vulnerabilities.
- Checking the application against the OWASP Top Ten categories.
- Checking the application using the OWASP Web Security Testing Guide.
The aim is to minimize security risks during development rather than reacting after the fact.
Why OWASP is important?
OWASP has established itself as the international standard for secure software development. Its principles and best practices are transparent, open, and practical—ideal for integrating security firmly into the development process.
By using and adhering to these guidelines:
- security vulnerabilities are detected early on,
- the risk of successful attacks is significantly reduced,
- resilience to threats is increased,
- and the trust of customers and users in the applications is strengthened.
Your contact person at imbus
Mr. Tobias Esser
mail: security@imbus.de
phone: +49 221 998788-0
fax: +49 221 998788-50
![[Translate to Englisch:] [Translate to Englisch:]](/fileadmin/_processed_/9/6/csm_Security_Test_Header_f0a8b4b688.jpg)